Suspected Outbound Traffic on a WHM/cPanel Server – Initial Checks
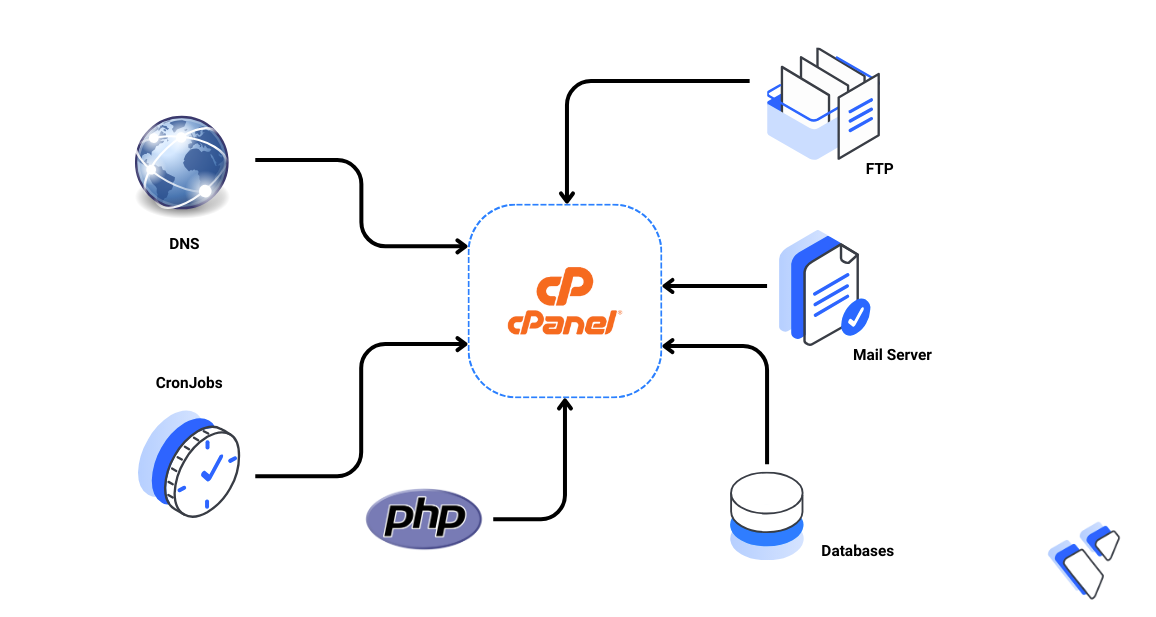
When unusual outbound traffic is suspected on a WHM/cPanel server, the issue should be approached methodically rather than jumping to conclusions. Outgoing traffic problems are often related to compromised accounts, misconfigured services, or abused scripts rather than the operating system itself.
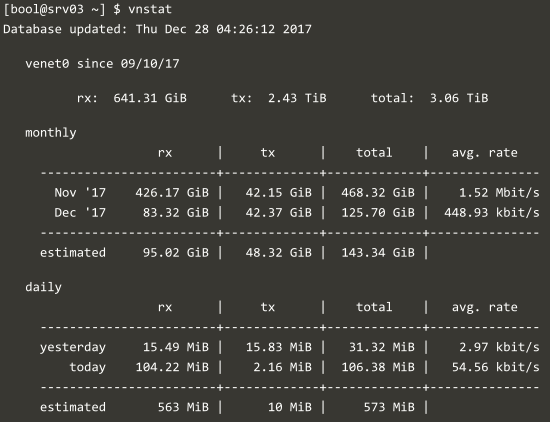
1. Check Overall Network Usage
Start by reviewing the server's network statistics to confirm whether outbound traffic is actually abnormal.
-
Monitor real-time traffic usage
-
Compare inbound vs outbound traffic
-
Identify sudden or sustained spikes
This helps determine whether the issue is temporary, scheduled, or potentially malicious.
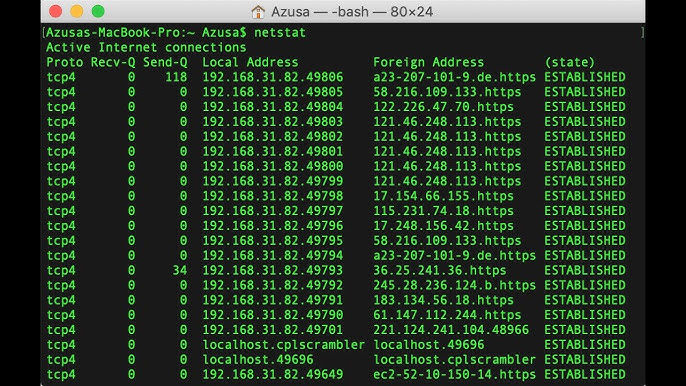
2. Identify Active Connections
Review active and established network connections to understand where traffic is going.
-
List outbound connections and destination IPs
-
Identify processes maintaining long-lived connections
-
Check for unusual external IP addresses or ports
Unexpected destinations are often the first red flag.
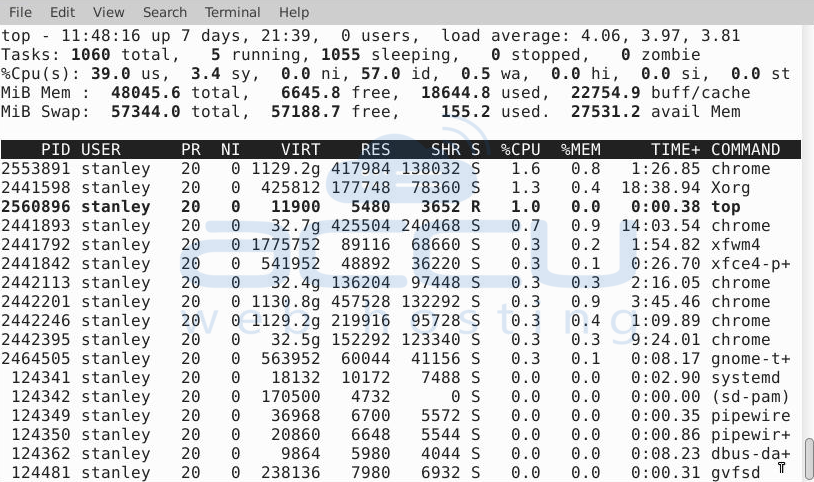
3. Review Running Processes
Analyze currently running processes and their resource usage.
-
Look for unknown or suspicious processes
-
Check processes running under user accounts
-
Verify services consuming network resources
Compromised user-level processes are far more common than root-level breaches.
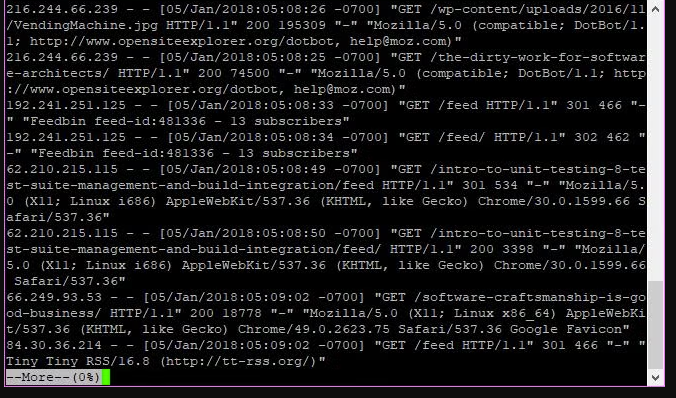
4. Inspect Web Server Activity
Web-based scripts are a frequent source of outbound traffic.
-
Review Apache/Nginx access logs
-
Look for excessive POST requests
-
Identify scripts making external requests (API calls, curl, wget)
Poorly written or abused PHP scripts can easily generate outbound traffic.
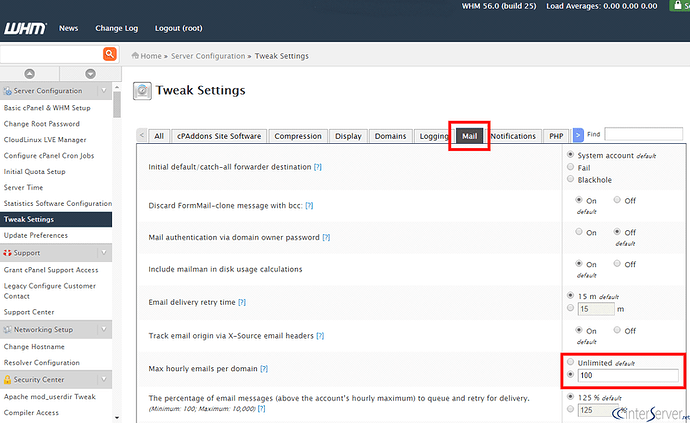
5. Check Mail Services
Mail services are one of the most common causes of outbound traffic.
-
Review mail queue size
-
Inspect outgoing mail logs
-
Look for spam patterns or unknown sender domains
Even a single compromised account can generate significant outbound traffic.
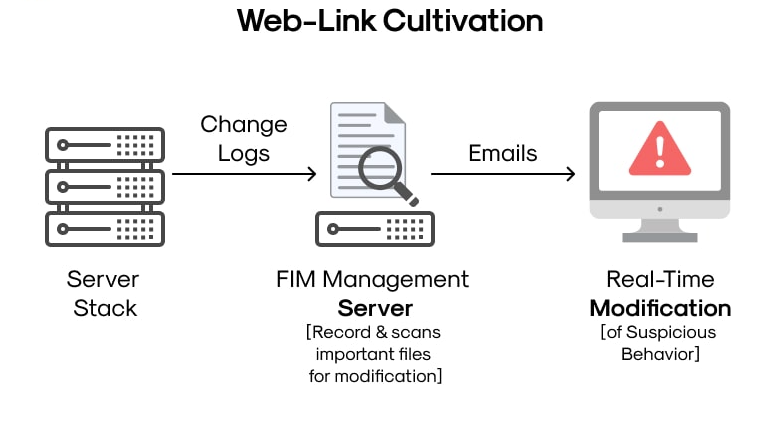
6. Verify User Accounts and File Integrity
Inspect user directories for unauthorized or modified files.
-
Look for recently changed files
-
Scan for obfuscated or encoded scripts
-
Check file permissions and ownership
Malicious scripts are often hidden in writable directories.
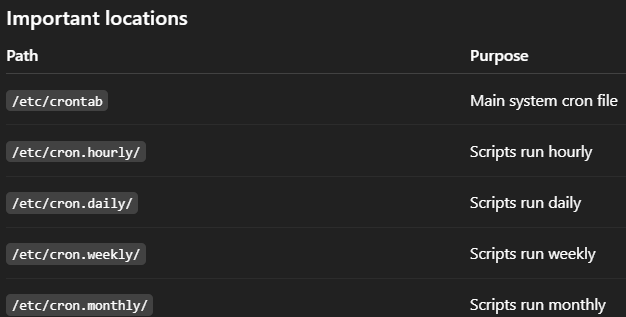
7. Review Cron Jobs
Cron jobs are frequently overlooked.
-
Check system-wide and user-level cron jobs
-
Look for unfamiliar or suspicious scheduled tasks
-
Verify execution frequency
Attackers often rely on cron to maintain persistence.
Conclusion
When outbound traffic is suspected on a WHM/cPanel server, the key is structured analysis rather than panic. Most issues originate from compromised user accounts, abused scripts, or mail services. By following a clear checklist, administrators can quickly identify the root cause and take corrective action before the problem escalates.